

Users require secure, instantaneous, and private methods to share large files and sensitive communications without relying on centralized cloud providers that often compromise privacy or throttle bandwidth.
Design and engineer a decentralized intelligence architecture capable of establishing secure P2P connections for real-time data streaming and encrypted communication within a serverless ecosystem.
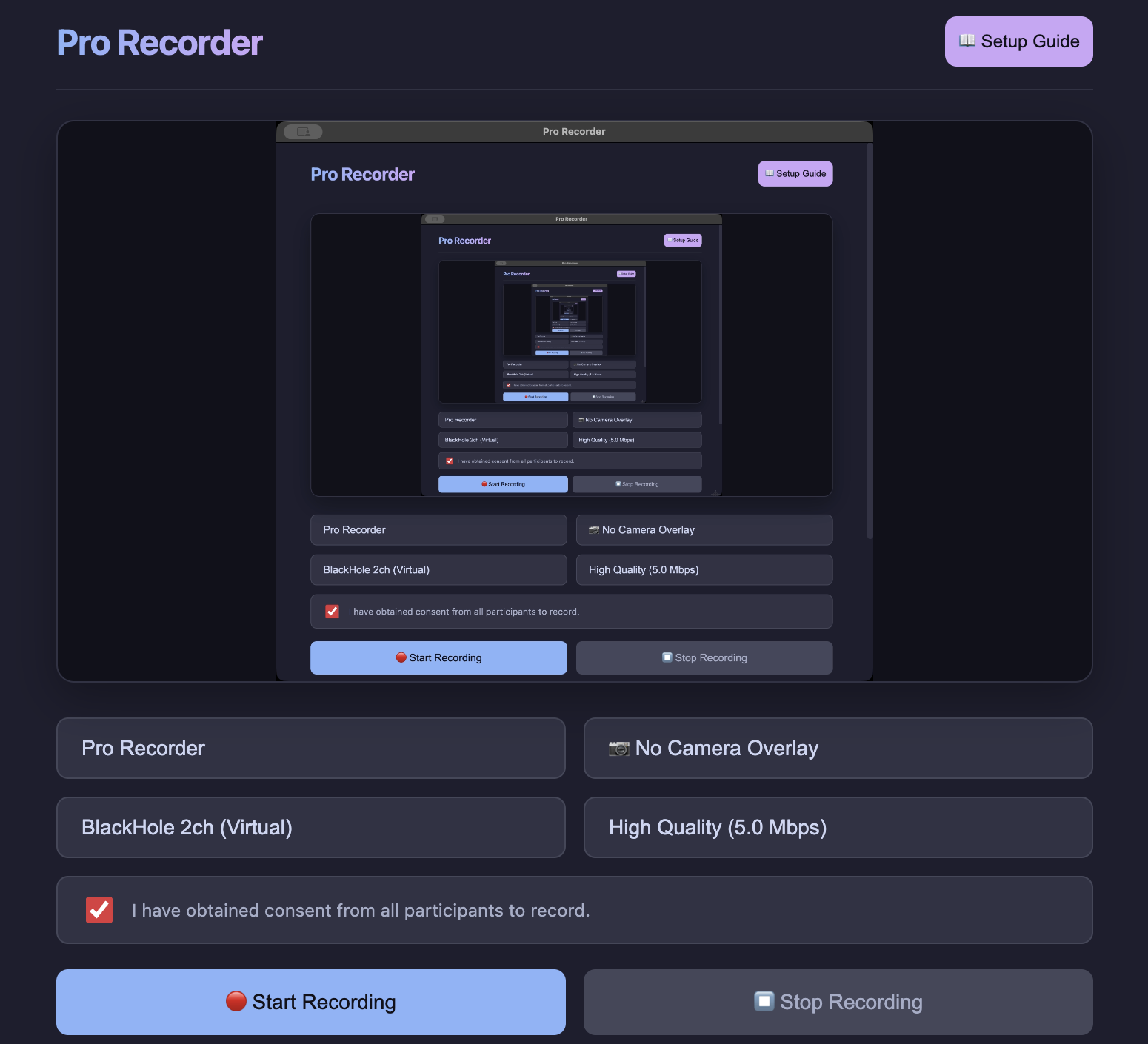
Standard recording software often stores video data in temporary memory (RAM), causing catastrophic data loss and system crashes during multi-hour marathon meetings or high-resolution screen captures.
Develop a robust, professional-grade desktop recording utility capable of sustained high-bitrate capture while ensuring data integrity and cross-platform compatibility without professional code-signing overhead.
Users require more organic, persistent, and capable AI systems that move beyond basic text interfaces to integrate seamlessly across devices with real-time, human-like interaction and deep contextual awareness.
Design and build a next-generation intelligence architecture capable of real-time voice interaction, long-term cognitive memory retention, and complex multimodal processing within a secure ecosystem.
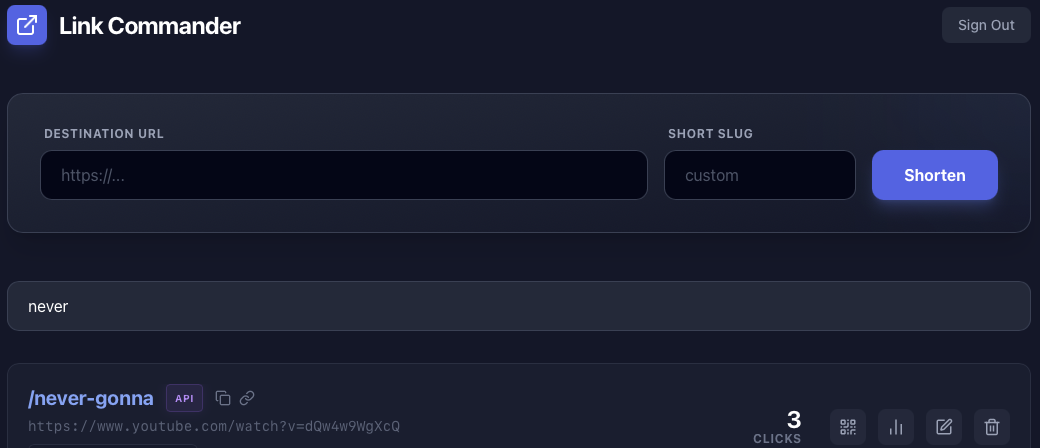
In today's digital landscape, long URLs are cumbersome to share across platforms with character limits like Twitter, SMS, and messaging apps. Users needed a simple, reliable way to create clean, professional-looking short links.
Build a web-based URL shortening service that generates compact, memorable links while maintaining reliable redirection to original destinations, with minimal user friction.

In an era of increasing data breaches and privacy concerns, users needed a secure way to share sensitive information like passwords, API keys, and confidential messages without leaving permanent digital traces in chat logs or email history.
Create an ephemeral messaging platform that enables secure, one-time message delivery with automatic self-destruction after viewing, ensuring zero data retention and maximum privacy.
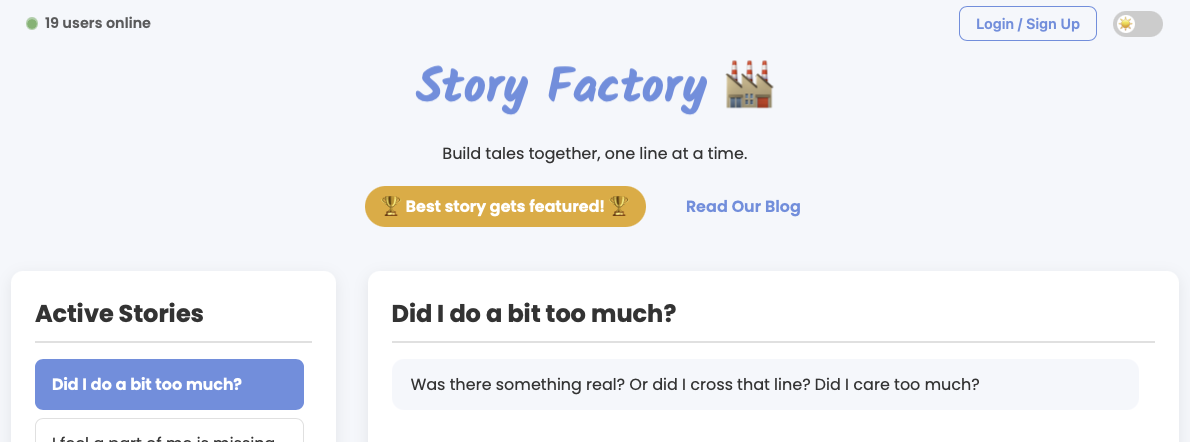
Creative writers often work in isolation, lacking platforms for real-time collaborative storytelling. Existing writing platforms didn't offer an engaging, gamified experience for building narratives collectively with a community of writers.
Build an interactive collaborative storytelling platform that enables users to co-create narratives one line at a time, with community engagement features and a structured story lifecycle management system.
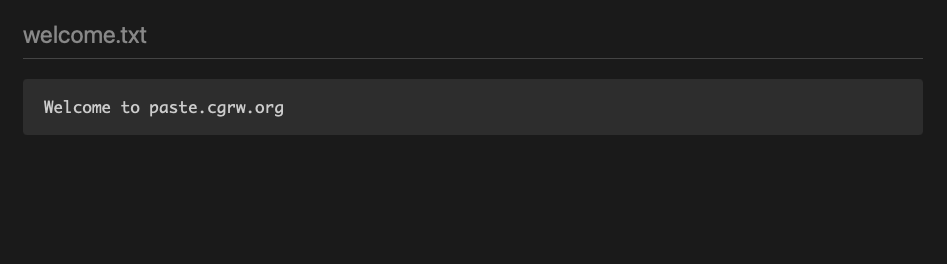
Public pastebin services posed security risks for sharing sensitive code, configuration files, and confidential documentation. Users needed a private, secure alternative with encryption capabilities and controlled access for sharing technical information.
Develop a private code hosting service with read-only architecture, password protection, and encryption support for secure sharing of sensitive technical content without social features or distractions.
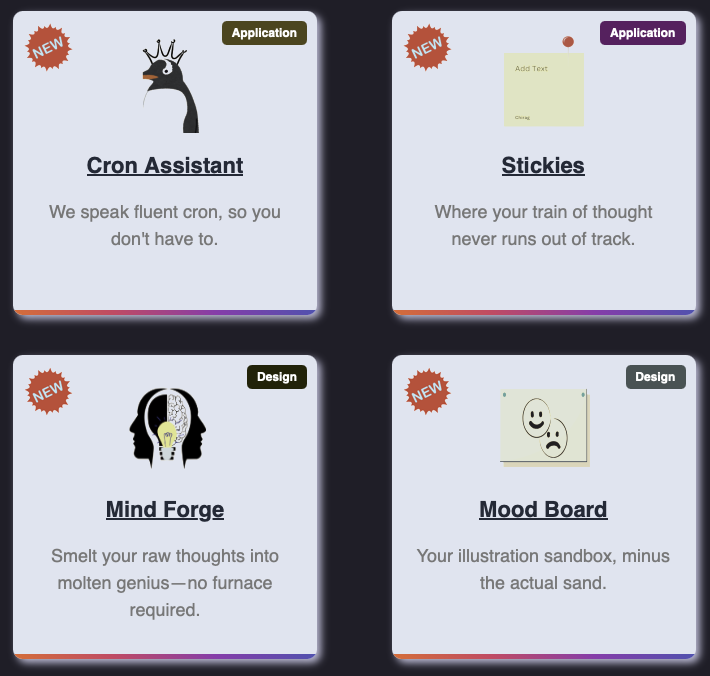
Users frequently needed to access multiple online tools for various tasks - from development utilities to security checks, file conversions to AI services - requiring navigation across numerous websites with inconsistent interfaces and reliability.
Create a comprehensive, centralized digital toolbox aggregating diverse browser-based utilities across multiple categories into a single, unified platform with consistent user experience and instant access.
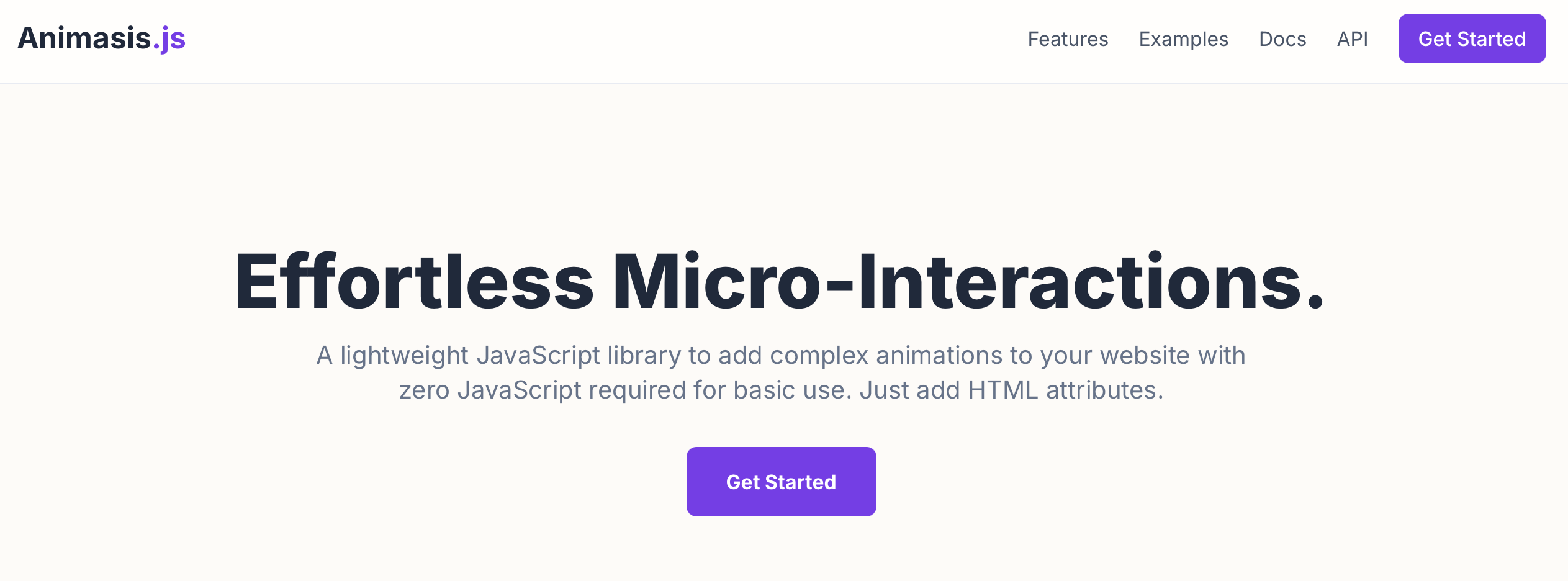
Web developers needed a simple way to add complex animations to websites without writing extensive JavaScript code or managing heavy animation libraries. Existing solutions were either too complex or required significant dependencies.
Build a lightweight, dependency-free JavaScript animation library that enables complex trigger-based animations using simple HTML data attributes, with support for hover, click, and scroll triggers.
Security professionals need hands-on experience with diverse security architectures, attack vectors, and mitigation strategies, but lack safe environments to practice without risking production systems or violating compliance requirements.
Design and maintain an evolving home lab infrastructure that simulates enterprise-grade security environments with vulnerable systems for attack practice, mitigation testing, and cross-platform administration across on-premises and cloud infrastructures.

Food wastage at events contrasted with food insecurity in communities created a critical social challenge. There was no efficient system to connect surplus food from events with people in need, and communities lacked a platform to discuss and coordinate food distribution efforts.
Build a full-stack web application as part of an 8-member team to facilitate excess food distribution from events to those in need, with integrated community blogging features to foster engagement and awareness.

Traditional PIN-based authentication systems were vulnerable to shoulder surfing, keylogging, and credential theft. Biometric authentication needed innovative approaches that were both secure and user-friendly, with eye movement patterns offering a unique behavioral biometric solution.
Lead a 4-member team to develop a continuous authentication system using gaze pattern monitoring as a behavioral biometric PIN, achieving high accuracy in user identification while reducing unauthorized access incidents.

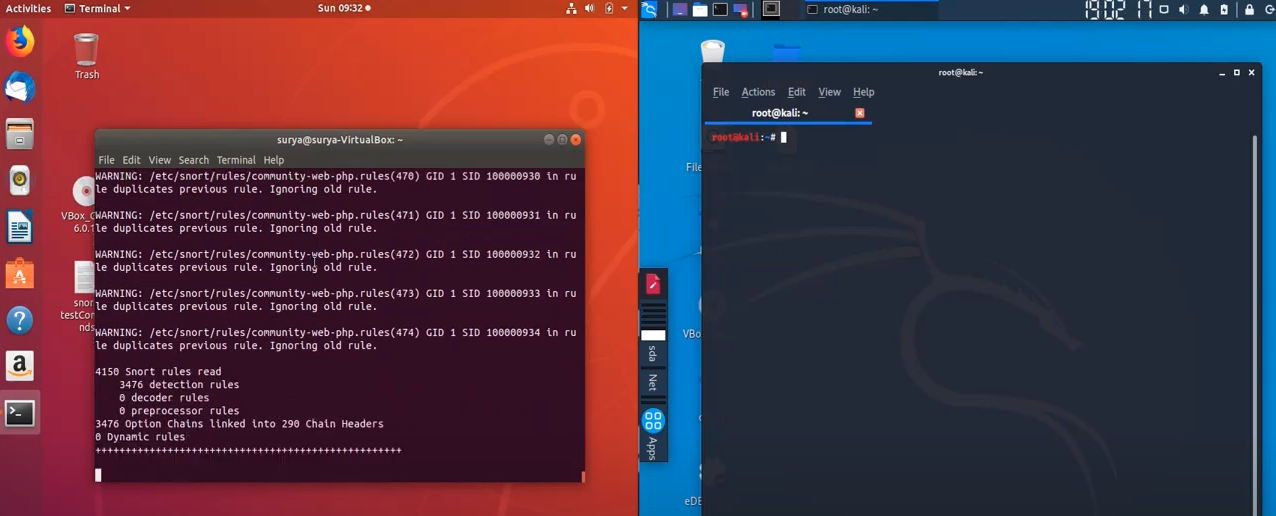
Network security systems faced increasing sophistication of cyber threats, with traditional intrusion detection systems struggling to identify novel attack patterns while generating excessive false positives that overwhelmed security teams.
Develop an advanced Intrusion Detection System using layered machine learning algorithms to enhance threat detection accuracy while minimizing false positives, as part of a 4-member collaborative team project.
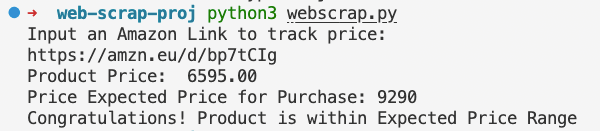
Online shoppers struggled to monitor price fluctuations on Amazon products, often missing optimal purchase windows. Manual price checking was time-consuming, and users needed an automated way to track products against their budget constraints.
Build an automated price tracking system using web scraping to monitor Amazon product prices and alert users when prices fall within their specified budget range.
Developers faced challenges maintaining up-to-date Node.js package versions across projects. Manual version checking was tedious, and outdated packages posed security risks and missed performance improvements. Automated version monitoring and update solutions were needed.
Create an automated surveillance tool that fetches Node package versions from GitHub repositories (both private and public), compares them with installed versions, and enables automatic updates with pull request creation.

E-commerce platforms faced growing security concerns regarding customer data protection, payment information breaches, and lack of end-to-end encryption in online transactions. Users needed a secure shopping platform with comprehensive data protection throughout the entire delivery pipeline.
Design and implement a secure e-commerce store with end-to-end encrypted delivery system, ensuring customer data and transaction information remain protected from browsing to order fulfillment.

Backend API development often involved complex frameworks with steep learning curves and overhead. Developers needed a lightweight, performant API solution for managing user and post data without unnecessary complexity or bloat.
Build a minimalist backend API using GoLang and MongoDB that efficiently handles User and Post attributes with clean architecture, high performance, and simple deployment.

Climate change research required comprehensive analysis of historical temperature data to understand global warming patterns. Scientists and researchers needed accessible tools to analyze and visualize Earth's surface temperature changes over time using scientific computing methods.
Conduct a scientific study analyzing climate change impacts on Earth's surface temperature using Python and Jupyter Notebook for data processing, statistical analysis, and visualization of temperature trends.
Security monitoring and automated surveillance systems required reliable motion detection capabilities. Traditional security cameras lacked intelligent motion sensing, creating a need for accessible, software-based motion detection solutions using standard webcam hardware.
Develop a real-time motion detection system using Python that can detect movement of objects in front of a standard webcam, with applications in security monitoring and automated surveillance.